When you submit an Other Transaction Authority (OTA) proposal, your technical solution and innovation are only part of the story. The other part, the one that often determines who gets selected, is how well you demonstrate security maturity through documented, verifiable evidence.
Evaluators reviewing OTA submissions are not just asking, “Is this technology impressive?” They are also asking, “Can we trust this company to handle sensitive data safely?” Understanding what kind of security evidence sponsors expect will help your proposal stand out for the right reasons.
Sponsors Want Proof, Not Promises
A common mistake in OTA proposals is assuming that general statements about cybersecurity are enough. Phrases like “we follow NIST guidelines” or “our systems are compliant with DFARS 7012” sound good but do not prove anything.
Sponsors are looking for evidence, not intentions. They expect to see clear documentation, specific controls, and measurable performance. The goal is to demonstrate that your team has already built a secure foundation before the contract begins.
1. Documented Compliance Framework Alignment
Most OTA projects involve handling at least some Controlled Unclassified Information (CUI) or export-controlled data. That means sponsors want to see alignment with established frameworks such as NIST SP 800-171, DFARS 252.204-7012, and in some cases, CMMC 2.0.
Strong proposals include:
- A completed or in-progress System Security Plan (SSP)
- A Plan of Actions and Milestones (POA&M), if any gaps exist
- A summary describing how your organization maintains continuous monitoring
These documents tell evaluators that your team is not just aware of compliance but actively managing it.
2. Evidence of Secure Infrastructure
Sponsors also expect to see evidence that your infrastructure can protect mission data. This may include:
- Current vulnerability scan reports or penetration test summaries
- Details on how multi-factor authentication and encryption are enforced
- Network diagrams showing segmentation of development and production environments
- Cloud compliance certifications (such as FedRAMP or equivalent)
You do not need to include sensitive internal data, but you should show that security has been implemented, not merely promised.
3. Incident Response and Data Protection Procedures
Evaluators want to know what will happen if something goes wrong. A short, clearly written Incident Response Plan is valuable evidence. It should show how your team detects, reports, and mitigates incidents.
Many contractors also include a Data Protection Policy that outlines how access is granted, how data is stored, and how removable media and portable devices are controlled. These details build trust with evaluators who are assessing risk as much as they are assessing innovation.
4. Staff Training and Access Control
Your people are part of your security evidence. Sponsors expect to see that everyone handling OTA-related data has completed regular cybersecurity awareness training. They also look for clear access control measures, such as:
- Role-based permissions
- Background checks for staff with CUI access
- Documented offboarding procedures for employees and subcontractors
This level of human-layer security shows maturity and discipline, both of which evaluators associate with lower project risk.
5. Secure Development and Testing Practices
If your OTA project involves software, sponsors expect documentation of your software development lifecycle (SDLC) security practices. That includes:
- Code review and approval processes
- Use of secure repositories and version control
- Vulnerability scanning in development and staging environments
- Patch management and update policies
This shows that security is integrated into your engineering culture rather than tacked on at the end.
6. Evidence of Past Performance and Third-Party Validation
One of the strongest forms of evidence is external validation. Sponsors take notice when a proposal includes references to:
- Successful audit results
- CMMC readiness assessments
- Security certifications or third-party attestations
Even a summary of a recent compliance assessment can increase your credibility. Evaluators prefer teams that can show a track record of delivering secure solutions, not just promise to do so in the future.
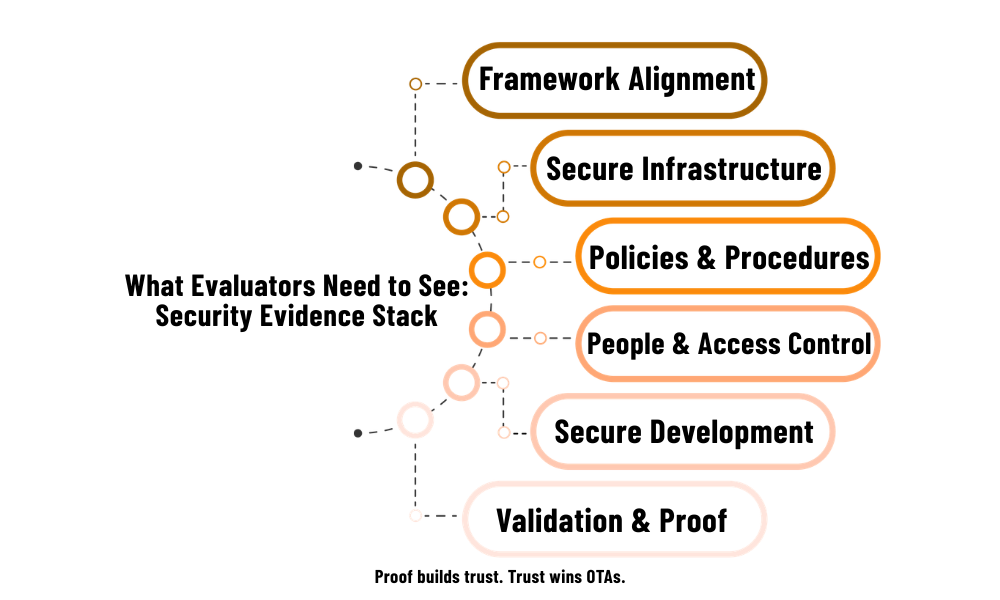
Putting It All Together
A competitive OTA proposal presents security as part of the overall value proposition. It shows that your team can innovate quickly without compromising protection. The evidence need not be exhaustive, but it should demonstrate that your organization is now ready to safeguard government data.
At a minimum, every proposal should include:
- A security framework summary (NIST, DFARS, or CMMC alignment)
- Documentation of key policies and procedures
- Evidence of secure infrastructure and access control
- References or reports verifying your compliance posture
These elements give evaluators the confidence to choose you over less-prepared competitors.
Next Step
Before you submit your next OTA proposal, download Black Rock’s Tech Modernization Checklist. It will help you verify your systems, assess security readiness, and confirm that you have the documentation sponsors expect to see.