When speed and innovation drive the mission, security can feel like the one factor holding everything back. For defense programs operating under an Other Transaction Authority (OTA), the challenge is clear: move fast enough to deliver results while remaining secure enough to meet the Department of Defense’s expectations.
For Chief Information Security Officers (CISOs) and program leads, that balance is not optional. All Federal Acquisition Regulations may not apply to the prototype phase, but the risks to data, systems, and compliance are just as real.
At Black Rock Engineering & Technology, we manage an active OTA designed to accelerate modernization securely. Here is how CISOs can protect sensitive work during the OTA prototype phase without slowing progress.
Start with a Security Architecture, Not a Checklist
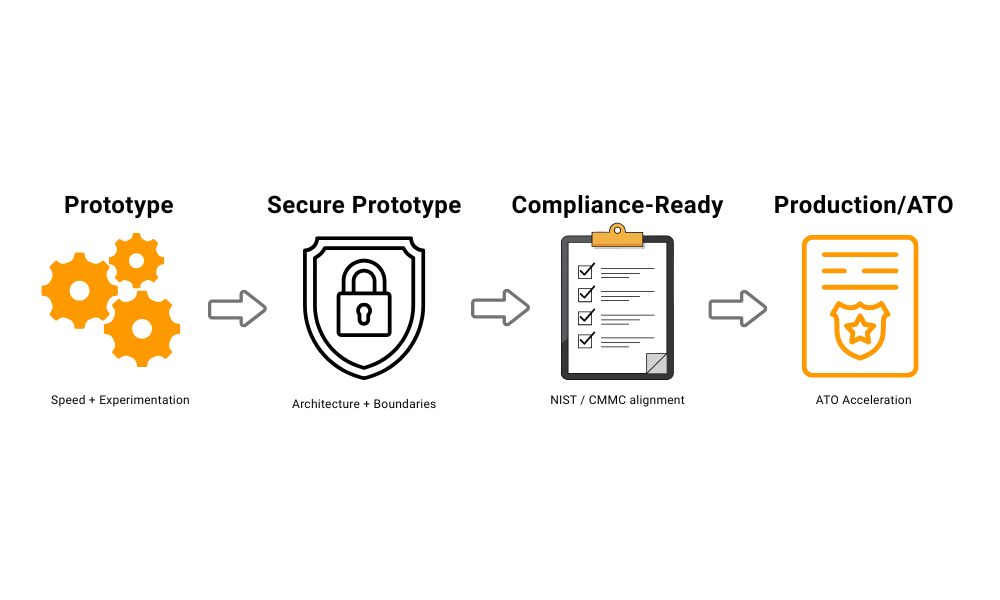
Prototypes often begin as technical experiments, but they quickly become operationally relevant. That transition is where many programs get exposed. CISOs should build a lightweight, scalable security architecture from day one, even if the complete compliance baseline will come later.
A practical starting point includes:
- Defining what data will be processed, stored, or transmitted.
- Mapping system boundaries and access points early.
- Using secure-by-design principles, not bolt-on controls after the fact.
The goal is not to implement every compliance control immediately, but to build an architecture that can evolve into full compliance as the project progresses.
Align With NIST 800-171 and CMMC from the Start
OTAs move faster because they bypass specific administrative steps, but they do not bypass cybersecurity requirements. If a prototype handles Controlled Unclassified Information (CUI), it still falls under NIST 800-171 and CMMC expectations.
CISOs should embed these standards early, using simplified compliance tracking and automated reporting. The faster you document your controls, the easier it becomes to transition to full Authority to Operate (ATO) later.
At Black Rock, we help OTA participants align with these frameworks from the start, so compliance becomes a continuous process rather than a project milestone.
Protect Collaboration Environments
OTA prototypes often involve multiple organizations, including startups, research institutions, and integrators. That collaboration can introduce serious risk if handled informally. CISOs should ensure that every participating partner operates within a controlled digital environment that meets baseline security standards.
Use vetted collaboration platforms that support government-grade encryption, identity management, and access controls. Require each partner to validate their own system security before data exchange begins. A single weak link can compromise the entire prototype effort.
Automate Where Possible
Manual security reviews and reporting can slow down development. To maintain speed, automate what you can. Automated patch management, vulnerability scanning, and configuration monitoring allow teams to move quickly while maintaining visibility into risk.
Continuous monitoring solutions and compliance-as-code frameworks reduce delays by embedding security directly into development and deployment pipelines. This approach helps teams keep prototypes both agile and secure.
Keep Security Integrated in the Prototype-to-Production Transition
A successful prototype often becomes the foundation for production. When that transition happens, the security groundwork laid during the OTA phase determines how fast you can scale.
CISOs should maintain complete documentation of controls, vulnerabilities, and fixes throughout the prototype cycle. That record becomes the backbone of the security package required for Authority to Operate or full production authorization.
At Black Rock, we guide our OTA participants through this transition, ensuring their systems meet DoD security and compliance requirements without losing momentum.
The Bottom Line
Security should never be the reason an innovation fails to deploy, but it must be part of every decision that enables deployment. For CISOs working under an OTA, the key is balance: move fast while ensuring the proper safeguards are in place.
By building a security architecture early, embedding compliance from the start, and leveraging automation, CISOs can deliver prototypes that are secure, scalable, and ready for the mission.
If your organization is developing a prototype under an OTA and needs to strengthen security without losing speed, schedule a call with Black Rock Engineering & Technology.
Our OTA ecosystem gives innovators a clear path to deliver results securely and confidently.
Appendix / References
- NIST – SP 800-171 Rev. 2, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations
- CMMC Accreditation Body – Cybersecurity Maturity Model Certification Framework
- DoD – Other Transaction Authority (OTA) Guide
- CISA – Zero Trust Maturity Model
- GAO – DoD Use of Other Transactions for Prototype Projects Has Increased (gao.gov)
