For defense innovators, Other Transaction Authorities (OTAs) have become the fastest way to collaborate with the Department of Defense. They let technology companies, research teams, and nontraditional contractors move ideas from prototype to production more rapidly than traditional contracting ever could.
But faster does not mean easier. While OTAs offer flexibility in acquisition, they do not absolve the responsibility of securing data, protecting systems, or meeting compliance standards. Every OTA participant must still prove that their environment can safeguard information critical to national security.
At Black Rock Engineering & Technology, we operate an active OTA designed for secure modernization. Here is what every partner needs to know about the cyber requirements that govern OTA work and how to meet them efficiently.
Cybersecurity Is Still Mandatory
OTAs may bypass sections of the Federal Acquisition Regulation, but they do not exempt participants from cybersecurity compliance. If your prototype, system, or project processes government data, connects to DoD networks, or handles Controlled Unclassified Information (CUI), you are subject to the exact federal cybersecurity requirements as any prime contractor.
Those include:
- NIST SP 800-171 for protecting CUI in nonfederal systems.
- DFARS 252.204-7012 clauses that require reporting cyber incidents within 72 hours.
- CMMC certification for contractors handling sensitive data.
These frameworks define how your systems must be secured, monitored, and validated. Even in a flexible OTA environment, you cannot skip them.
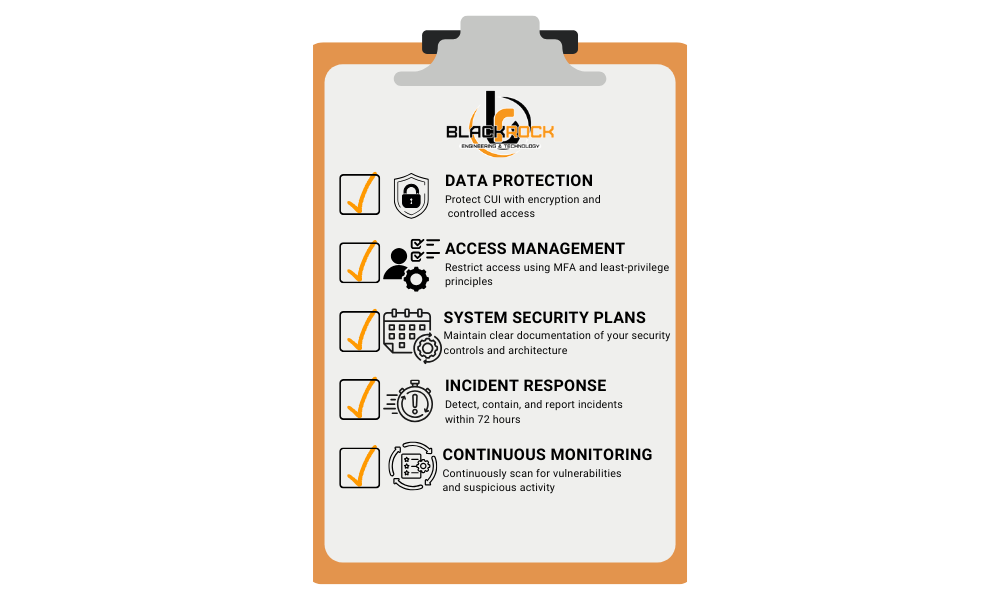
Understanding the Core Requirements
Most OTA programs include language that references or mirrors NIST and DFARS requirements. Whether written directly into the agreement or handled through your subcontractor relationship, these are the key expectations every participant should plan for:
- Data Protection: Encrypt data in transit and at rest. Identify which information qualifies as CUI and apply appropriate access control and monitoring.
- Access Management: Implement multi-factor authentication and least-privilege principles across all environments that touch federal data.
- System Security Plans (SSPs): Maintain a living document describing your network architecture, security controls, and implementation methods.
- Incident Response and Reporting: Be ready to identify, contain, and report any cyber incidents within the required 72-hour window.
- Continuous Monitoring: Use automated tools to detect configuration drift, vulnerabilities, and suspicious behavior.
These controls are not just technical; they are contractual. If a breach or audit reveals missing protections, the entire OTA effort can be delayed or terminated.
How to Meet Requirements Without Slowing Progress
Security often feels like a trade-off with speed, but it doesn’t have to be. The key is to make cybersecurity part of your build process, not a separate task that comes later.
CISOs and project leads should:
- Adopt a “security-first” architecture that aligns with NIST 800-171 but scales with project size.
- Leverage secure cloud environments already approved for federal workloads, such as FedRAMP Moderate or High.
- Automate compliance tracking through configuration management and vulnerability scanning tools.
- Document continuously, not just at milestones. This reduces the work required for ATO or follow-on production transitions.
At Black Rock, we help partners integrate these practices from day one, so security and compliance never slow down delivery.
What Black Rock Provides to OTA Partners
Black Rock’s OTA ecosystem was built to make cybersecurity straightforward for participating organizations. We provide:
- A secure collaboration environment for partners exchanging CUI and prototype data.
- Guidance and templates for efficiently meeting NIST, DFARS, and CMMC controls.
- Compliance monitoring and readiness assessments aligned with DoD standards.
- Support during audits or ATO transitions to ensure a smooth path from prototype to production.
Our goal is to give OTA participants the freedom to innovate without worrying that compliance gaps will derail progress.
The Bottom Line
Cybersecurity is not optional in OTA work. The same rules that protect sensitive DoD data apply to every project, regardless of the contracting path.
The difference lies in execution. By integrating compliance early, automating where possible, and partnering with experienced guides, innovators can stay secure while moving at the speed of mission need.
If your organization is building or collaborating under an OTA, with Black Rock Engineering & Technology. We will help you meet every cybersecurity requirement with confidence and keep your innovation mission-ready.