When a defense organization enters an Other Transaction Authority (OTA) effort, speed and collaboration increase immediately, but so does risk. OTAs often rely on consortia, subcontractors, and niche vendors that have not worked together before. That puts the CISO in a critical position.
From the sponsor’s perspective, a single weak vendor can compromise the entire effort. From the CISO’s perspective, the question becomes simple but serious: How do we evaluate vendors and subs fast without lowering our security standards?
Why Vendor Evaluation Matters More in OTAs
OTAs are designed for rapid prototyping and experimentation. That flexibility often means looser structures and faster partner onboarding. While this accelerates innovation, it also quickly expands the attack surface.
Unlike traditional contracts, OTA teams are often assembled specifically for one project. That means trust is assumed before it is proven. CISOs must compensate by applying disciplined evaluation early, before data is shared or systems are connected.
Start with Data Exposure, Not Company Size
One of the most common mistakes CISOs make is evaluating vendors based on reputation or scale. In OTA environments, size matters far less than what data the vendor will touch.
The first evaluation question should always be:
What type of data will this vendor access?
If the answer includes Controlled Unclassified Information, export-controlled data, or operational mission data, the bar must be high. Vendors who only contribute tooling or analytics may require lighter controls. Risk should always be tied to exposure.
Verify Framework Alignment Early
OTA vendors do not get a free pass on cybersecurity. Sponsors still expect alignment with DFARS 252.204-7012 and NIST SP 800-171 when CUI is involved.
CISOs should request concrete evidence, not verbal assurances. That includes:
- A System Security Plan or equivalent summary
- A description of implemented controls
- Any open gaps with mitigation timelines
If a vendor cannot articulate their security posture clearly, they are not ready to have an OTA team handle sensitive data.
Evaluate Access Controls and Segmentation
In OTA teams, vendors often need limited access, not full system visibility. CISOs should assess whether each vendor can support least-privilege access.
Key questions include:
- Can role and project restrict access?
- Are development, test, and production environments segmented?
- Is multi-factor authentication enforced consistently?
Vendors who require broad or permanent access to perform limited functions introduce unnecessary risk.
Assess Incident Response Readiness
Speed cuts both ways. If something goes wrong in an OTA environment, response time matters. CISOs should confirm that vendors have documented incident response procedures and understand government reporting requirements.
This includes familiarity with reporting timelines, escalation paths, and coordination with the prime contractor. Vendors who cannot respond quickly and transparently create operational and contractual risk.
Look Beyond Tools to People and Process
Security posture is not just about technology. CISOs should assess whether vendor personnel handling sensitive data are trained, vetted, and accountable.
Important considerations include:
- Security awareness training frequency
- Background checks where required
- Defined onboarding and offboarding processes
Strong processes reduce the likelihood of human error, which remains one of the most common causes of security incidents.
Ensure IP and Data Rights Are Understood
From a security standpoint, unclear data rights create confusion about who can store, copy, or reuse sensitive information. CISOs should work closely with legal and contracting teams to ensure vendors understand IP boundaries.
Vendors must know what data they can retain, for how long, and how it must be destroyed or returned at project close. Ambiguity here increases both security and legal exposure.
Balance Speed with Minimum Standards
CISOs are often under pressure not to slow the OTA effort. The goal is not to apply maximum controls everywhere, but to apply minimum acceptable standards consistently.
Clear onboarding requirements, standard evidence requests, and predefined access tiers allow vendors to be evaluated quickly without compromising security. Consistency is what preserves speed over time.
The Bottom Line
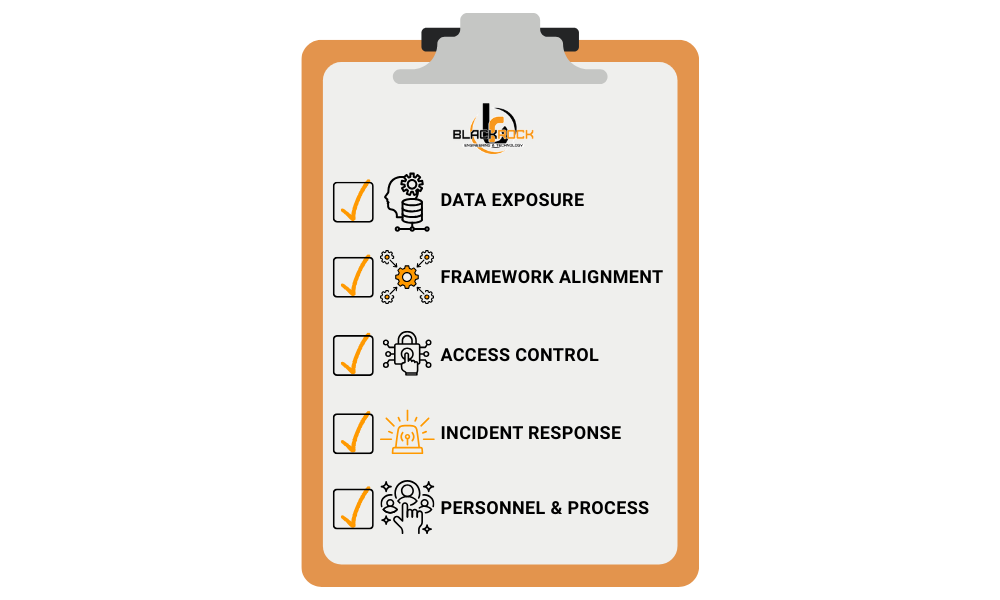
In OTA teams, vendors and subcontractors extend your security boundary whether you like it or not. CISOs who evaluate partners based on data exposure, framework alignment, access control, and response readiness protect both the mission and the organization.
The fastest OTA teams are not the ones that skip security. They are the ones who integrate it early and apply it intelligently.
Next Step
If you are building or joining an OTA team, download Black Rock’s Tech Modernization Checklist. It will help you assess vendor readiness, data exposure, and security posture before risk becomes reality.

